1 Password For El Capitan
I need to download the El Capitan to install on my Mac computer. What is the best place to download the El Capitan dmg or El Capitan iso.
Is this a good question?
Comments:
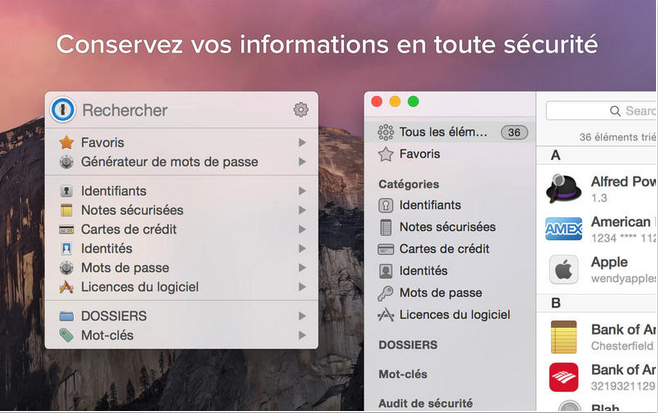
Aug 21, 2019 Mac OS X El Capitan 10.11.1 DMG Mac. Mac OS El Capitan was released to manufacturing on 20th September 2015, almost three and a half years ago. Its latest version 10.11.6 (15G22010) was released on 9th July 2018, almost 7 months ago. It runs on the platform including x86-64. Yes, 1Password 5.3 for Mac should be compatible with El Capitan and we are working on the upcoming 1Password 5.4 update that will be further optimized for El Capitan. The current plan is to have it out at the same time with El Capitan's release. If you'd like, you can run the latest beta of 1Password 5.4 on El Capitan.
I've been looking for El Capitan for weeks and today I finally managed to get it.
The Appstore no longer has OS X El Capitan available to download.
To solve this issue follow this link: http://bit.ly/ElCaptanOriginalOSX
.
The Appstore only has updates but not the original OS. So If you did not download El Capitan before it was removed from the App Store then you will not be able to get it from the Appstore anymore. You can now only download it via alternative sources, Just make sure they are trusted sources though. Hence I recommended the link above.
Hope this helps you also.
@Kate smith, They are illegally selling Apples software !
Find the official installers here
Infographic over the many versions of OSX/macOS
@katemor Its not true that App Store no longer has El Capitan as download. It does not have it as download, if your Apple-ID has never registered a machine with El Capitan. Otherwise they are still there.
And your link points to a place, which charges $20 for Apple software. Not quite legal..
About Apple security updates
For our customers' protection, Apple doesn't disclose, discuss, or confirm security issues until an investigation has occurred and patches or releases are available. Recent releases are listed on the Apple security updates page.
For more information about security, see the Apple Product Security page. You can encrypt communications with Apple using the Apple Product Security PGP Key.
Apple security documents reference vulnerabilities by CVE-ID when possible.
macOS Sierra 10.12.1, Security Update 2016-002 El Capitan, and Security Update 2016-006 Yosemite
Released October 24, 2016
AppleGraphicsControl
Available for: OS X Yosemite v10.10.5 and OS X El Capitan v10.11.6
Power cord for mac os mojave 15 inch 2014. Choose from: 30W USB-C Power Adapter,61W USB-C Power Adapter,96W USB-C Power Adapter,Apple 45W MagSafe 2 Power Adapter for MacBook Air. May 01, 2020 If you use a power adapter that is lower in wattage than the adapter that came with your Mac, it won't provide enough power to your computer. Mac notebooks that charge via USB-C come with an Apple USB-C Power Adapter with detachable AC plug (or 'duckhead'), and a USB-C Charge Cable. MacBook Pro (15-inch Core 2 Duo) MacBook Pro (17-inch Core 2 Duo) MacBook Pro (15-inch Glossy) MacBook Pro (17-inch) 45W MagSafe power adapter with MagSafe 2 style connector. MacBook Air (13-inch, 2017) MacBook Air (11-inch, Early 2015) MacBook Air (13-inch, Early 2015) MacBook Air (11-inch, Early 2014) MacBook Air (13-inch, Early 2014). IMac (Retina 5K, 27-inch, Late 2014 - 2015) iMac Pro (2017 and later) Mac Pro (2019). Apple 85W MagSafe Power Adapter (for 15- and 17-inch MacBook Pro) - Next Gallery Image; Apple 85W MagSafe Power Adapter (for 15- and 17-inch MacBook Pro) $79.00.
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A memory corruption issue was addressed through improved lock state checking.
CVE-2016-4662: Apple
AppleMobileFileIntegrity
Available for: macOS Sierra 10.12
Impact: A signed executable may substitute code with the same team ID
Description: A validation issue existed in the handling of code signatures. This issue was addressed through additional validation.
CVE-2016-7584: Mark Mentovai and Boris Vidolov of Google Inc.
Entry added November 27, 2016
AppleSMC
Available for: macOS Sierra 10.12
Impact: A local user may be able to elevate privileges
Description: A null pointer dereference was addressed through improved locking.
CVE-2016-4678: daybreaker@Minionz working with Trend Micro's Zero Day Initiative
ATS
Available for: macOS Sierra 10.12
Impact: Processing a maliciously crafted font file may lead to arbitrary code execution
Description: A memory corruption issue was addressed through improved memory handling.
CVE-2016-4667: Simon Huang of alipay, Thelongestusernameofall@gmail.com, Moony Li of TrendMicro, @Flyic
Entry updated October 27, 2016
ATS
Available for: macOS Sierra 10.12
Impact: A local user may be able to execute arbitrary code with additional privileges
Description: A memory corruption issue was addressed through improved memory handling.
CVE-2016-4674: Shrek_wzw of Qihoo 360 Nirvan Team
CFNetwork Proxies
Available for: macOS Sierra 10.12
1 Password For El Capitan Free
Impact: An attacker in a privileged network position may be able to leak sensitive user information
Description: A phishing issue existed in the handling of proxy credentials. This issue was addressed by removing unsolicited proxy password authentication prompts.
CVE-2016-7579: Jerry Decime
Core Image
Available for: OS X El Capitan v10.11.6
Impact: Viewing a maliciously crafted JPEG file may lead to arbitrary code execution
Description: A memory corruption issue was addressed through improved input validation.
CVE-2016-4681: Ke Liu of Tencent's Xuanwu Lab
Entry added October 25, 2016
CoreGraphics
Available for: macOS Sierra 10.12
Impact: Viewing a maliciously crafted JPEG file may lead to arbitrary code execution
Description: A memory corruption issue was addressed through improved memory handling.
CVE-2016-4673: Marco Grassi (@marcograss) of KeenLab (@keen_lab), Tencent
FaceTime
Available for: macOS Sierra 10.12
Impact: An attacker in a privileged network position may be able to cause a relayed call to continue transmitting audio while appearing as if the call terminated
Description: User interface inconsistencies existed in the handling of relayed calls. These issues were addressed through improved protocol logic.
CVE-2016-7577: Martin Vigo (@martin_vigo) of salesforce.com
Entry added October 27, 2016
FontParser
Available for: macOS Sierra 10.12
Impact: Parsing a maliciously crafted font may disclose sensitive user information
Description: An out-of-bounds read was addressed through improved bounds checking.
CVE-2016-4660: Ke Liu of Tencent's Xuanwu Lab
FontParser
Available for: macOS Sierra 10.12
Impact: Processing a maliciously crafted font file may lead to arbitrary code execution
Description: A buffer overflow existed in the handling of font files. This issue was addressed through improved bounds checking.
CVE-2016-4688: Simon Huang of Alipay company, thelongestusernameofall@gmail.com
Entry added November 27, 2016
IDS - Connectivity
Available for: macOS Sierra 10.12
Impact: An attacker in a privileged network position may be able to trick a user on a multi-party call into believing they are talking to the other party
Description: An impersonation issue existed in the handling of call switching. This issue was addressed through improved handling of 'switch caller' notifications.
CVE-2016-4721: Martin Vigo (@martin_vigo) of salesforce.com
Entry added October 27, 2016
ImageIO
Available for: OS X El Capitan v10.11.6
Impact: Parsing a maliciously crafted PDF may lead to arbitrary code execution
Description: An out-of-bounds write was addressed through improved bounds checking.
CVE-2016-4671: Ke Liu of Tencent's Xuanwu Lab, Juwei Lin (@fuzzerDOTcn)
ImageIO
Available for: OS X Yosemite v10.10.5 and OS X El Capitan v10.11.6
Impact: Processing a maliciously crafted image may result in the disclosure of process memory
Description: An out-of-bounds read issue existed in the SGI image parsing. This issue was addressed through improved bounds checking.
CVE-2016-4682: Ke Liu of Tencent's Xuanwu Lab
ImageIO
Available for: OS X El Capitan v10.11.6
Impact: A remote attacker may be able to execute arbitrary code
Description: Multiple out-of-bounds read and write issues exited in SGI parsing. These issues was addressed through improved input validation.
CVE-2016-4683: Ke Liu of Tencent’s Xuanwu Lab
Entry added October 25, 2016
Kernel
Available for: OS X Yosemite 10.10.5, OS X El Capitan 10.11.6, and macOS Sierra 10.12
Impact: A local user may be able to cause an unexpected system termination or arbitrary code execution in the kernel
Description: Multiple input validation issues existed in MIG generated code. These issues were addressed through improved validation.
CVE-2016-4669: Ian Beer of Google Project Zero
Entry updated November 2, 2016
Kernel
Available for: macOS Sierra 10.12
Impact: A local application may be able to execute arbitrary code with root privileges
Description: Multiple object lifetime issues existed when spawning new processes. These were addressed through improved validation.
CVE-2016-7613: Ian Beer of Google Project Zero
Entry added November 1, 2016
libarchive
Available for: macOS Sierra 10.12
1 Password For El Capitan 10
Impact: A malicious archive may be able to overwrite arbitrary files
Description: An issue existed within the path validation logic for symlinks. This issue was addressed through improved path sanitization.
CVE-2016-4679: Omer Medan of enSilo Ltd
libxpc
Available for: macOS Sierra 10.12
Impact: An application may be able to execute arbitrary code with root privileges
Description: A logic issue was addressed through additional restrictions.
CVE-2016-4675: Ian Beer of Google Project Zero
Entry updated March 30, 2017
ntfs
Available for: macOS Sierra 10.12
Impact: An application may be able to cause a denial of service
Description: An issue existed in the parsing of disk images. This issue was addressed through improved validation.
CVE-2016-4661: Recurity Labs on behalf of BSI (German Federal Office for Information Security)
NVIDIA Graphics Drivers
Available for: OS X Yosemite v10.10.5 and OS X El Capitan v10.11.6
Impact: An application may be able to cause a denial of service
Description: A memory corruption issue was addressed through improved input validation.
CVE-2016-4663: Apple
Security
Available for: macOS Sierra 10.12
Impact: A local attacker can observe the length of a login password when a user logs in
Description: A logging issue existed in the handling of passwords. This issue was addressed by removing password length logging.
CVE-2016-4670: Daniel Jalkut of Red Sweater Software
Entry updated October 25, 2016
Thunderbolt
Available for: macOS Sierra 10.12
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A null pointer dereference was addressed through improved input validation.
CVE-2016-4780: sweetchip of Grayhash
Entry added November 29, 2016
macOS Sierra 10.12.1 includes the security content of Safari 10.0.1.



